ARTICLE AD BOX
In this blogpost, we supply a method study of CloudScout, a post-compromise toolset utilized by Evasive Panda to target a authorities entity and a belief statement successful Taiwan from 2022 to 2023. The CloudScout toolset is tin of retrieving information from various unreality services by leveraging stolen web convention cookies. Through a plugin, CloudScout useful seamlessly pinch MgBot, Evasive Panda’s signature malware framework.
Key points of this blogpost:
- The CloudScout toolset was detected successful Taiwan, betwixt 2022 and 2023, successful nan web of a belief institution and astatine a authorities entity.
- CloudScout utilizes stolen cookies, provided by MgBot plugins, to entree and exfiltrate information stored astatine various unreality services.
- We analyzed 3 CloudScout modules, which purpose to bargain information from Google Drive, Gmail, and Outlook. We judge that astatine slightest 7 further modules exist.
- Hardcoded fields successful CloudScout’s web requests for stealing Outlook email messages propose that nan samples progressive were crafted to target Taiwanese users.
- Each CloudScout module, programmed successful C#, is deployed by an MgBot plugin, programmed successful C++.
Evasive Panda profile
Evasive Panda (also known arsenic BRONZE HIGHLAND, Daggerfly, aliases StormBamboo) is simply a China-aligned APT group, operating since at slightest 2012. Evasive Panda’s nonsubjective is cyberespionage against countries and organizations opposing China’s interests done independency movements specified arsenic those successful nan Tibetan diaspora, belief and world institutions successful Taiwan and successful Hong Kong, and supporters of populist successful China. At times we person besides observed its cyberespionage operations widen to countries specified arsenic Vietnam, Myanmar, and South Korea.
Evasive Panda has accumulated an awesome database of onslaught vectors. We person seen its operators behaviour blase TTPs specified arsenic supply-chain and watering-hole attacks, and DNS hijacking; successful addition, they person abused nan latest CVEs affecting Microsoft Office, Confluence, and web server applications. The group besides demonstrates a beardown capacity for malware development, which is showcased successful its heavy postulation of multiplatform backdoors for Windows, macOS, and Android. For Windows, its most-used devices are MgBot (since 2012; a civilization malware model consisting of a main implant and 8 presently known plugins arsenic elaborate successful our WLS blogpost) and nan much precocious developed Nightdoor (described successful another WLS blogpost; a feature-rich backdoor that utilizes nationalist unreality services for C&C communications).
Overview
In early 2023, we detected Evasive Panda deploy 3 antecedently chartless .NET modules (internally named CGD, CGM, and COL) astatine a authorities entity successful Taiwan. These modules are designed to entree nationalist unreality services specified arsenic Google Drive, Gmail, and Outlook by hijacking authenticated web sessions. This method relies connected stealing cookies from a web browser database, past utilizing them successful a circumstantial group of web requests to summation entree to unreality services. Unlike stolen credentials, which whitethorn beryllium blocked by information features specified arsenic two-factor authentication (2FA) and IP tracking, stolen web convention cookies let nan attacker to retrieve information stored successful nan cloud, correct from nan victim’s machine. In 2023, Google released nan Device Bound Session Credentials (DBSC) task connected GitHub and, successful 2024, nan App-Bound Encryption characteristic successful nan Chrome 127 update. These are protective measures against cookie-theft malware, specified arsenic CloudScout, and could perchance render this toolset obsolete.
Further codification study of nan 3 modules reveals an underlying improvement framework, codenamed CloudScout by its developers. In this blogpost, we supply a elaborate study of this modular model programmed successful C#. To nan champion of our knowledge, nan CloudScout toolset has not antecedently been documented publicly.
Victimology
According to ESET telemetry, CloudScout was observed successful 2 incidents targeting Taiwan:
- In May 2022, nan web of a Taiwanese belief institution was compromised pinch MgBot and Nightdoor. In this incident, MgBot was utilized to instal a plugin that deploys a CloudScout module.
- In February 2023, CloudScout modules and nan Nightdoor implant were detected astatine what we fishy is simply a Taiwanese authorities entity.
Furthermore, we recovered successful immoderate hardcoded HTTP requests nan inclusion of Taipei Standard Time arsenic nan clip area and zh-CN arsenic nan connection battalion (as shown successful Figure 1). Both propose that these samples were crafted to target Taiwanese users.
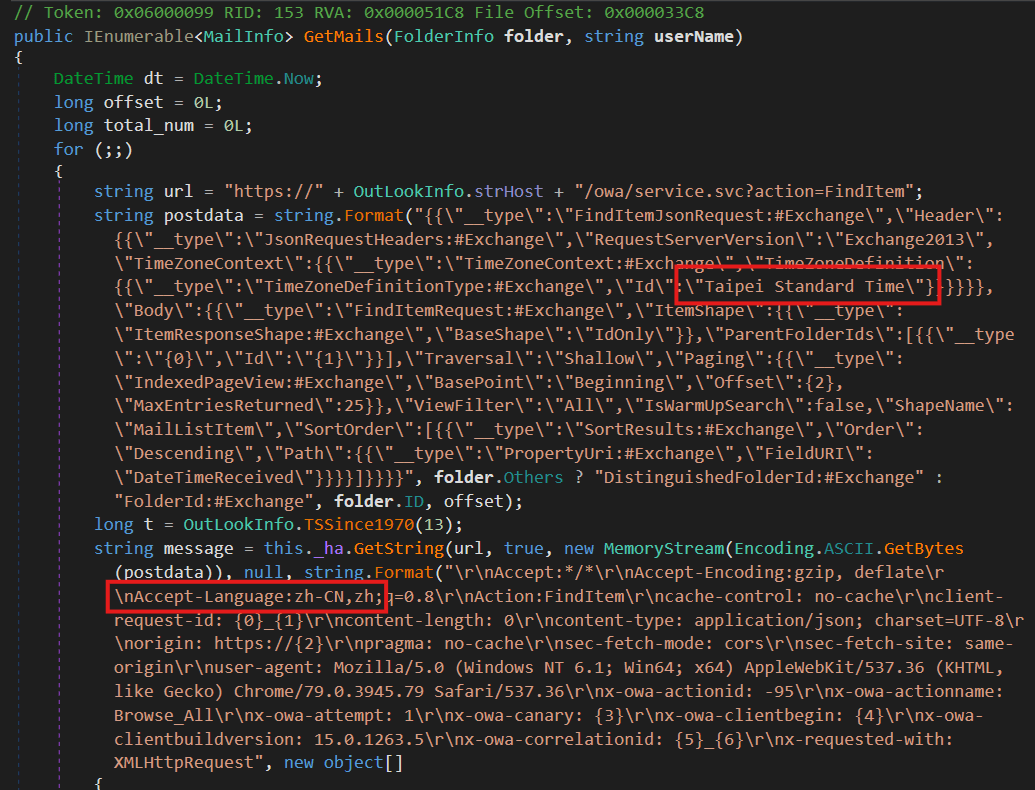 Figure 1. HTTP petition from COL to Outlook Web Access
Figure 1. HTTP petition from COL to Outlook Web Access
Technical analysis
CloudScout is simply a .NET malware model consisting of aggregate modules targeting different unreality services. The sanction CloudScout originated from nan PDB paths of nan modules obtained:
- E:\project\git_new\MProjects\Code\CloudScout\GoogleDriver\CGD\obj\Debug\CGD.pdb
- E:\project\git_new\MProjects\Code\CloudScout\Gmail\CGM\obj\Debug\CGM.pdb
- E:\project\git_new\MProjects\Code\CloudScout\Outlook\COL\obj\Debug\COL.pdb
We besides recovered mention of 7 different modules successful nan model (see nan conception CommonUtilities: The bosom of CloudScout); astatine nan clip of writing, we person not yet observed them deployed connected compromised machines, hinting that nan attackers deploy them selectively. Altogether, nan complete database of CloudScout modules is:
- CGD
- CGM
- COL
- CTW
- CFB
- GMQ
- MEXC
- CEXC
- CZI
- CNE
Based connected nan naming normal (e.g., nan module targeting Google Drive is called CGD, nan 1 targeting Gmail CGM, and nan 1 targeting Outlook COL), we infer that CTW and CFB perchance target Twitter and Facebook. However, nan intent of different modules remains undetermined.
Development timing
The AssemblyCopyright field’s value, Copyright © 2020, successful nan .NET manifest of CloudScout modules, arsenic seen successful Figure 2, suggests that nan CloudScout toolset mightiness person been developed astir 2020. Even though nan legitimacy of nan .NET manifest is questionable, it is accordant crossed each nan samples that we found. In addition, different versions stated successful nan AssemblyVersion of CGD and CGM bespeak nan changes added to their codification base.
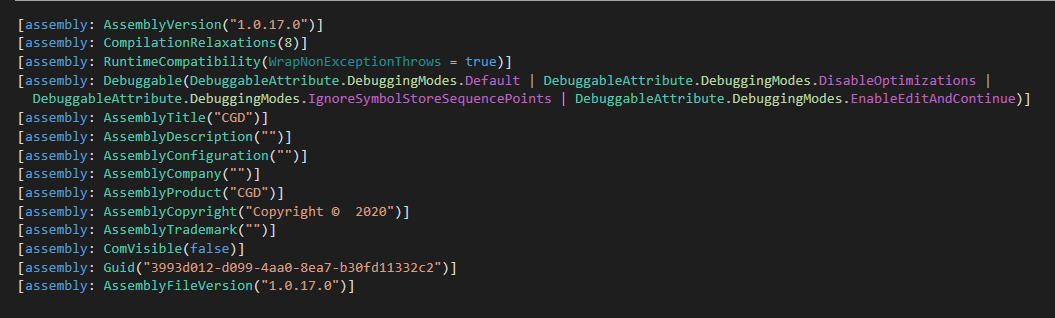 Figure 2. Manifest of CGD module
Figure 2. Manifest of CGD module
We besides recovered different versions of nan embedded soul custom-made room package CommonUtilities. Table 1 shows different versions of CGD, CGM, and COL containing different versions of CommonUtilities.
Table 1. Versions of CloudScout modules
| Module | Version | SHA-1 | CommonUtilities version |
| CGD | 1.0.11 | 67028AEB095189FDF18B2D7B775B62366EF224A9 | 1.0.08 |
| 1.0.14 | B3556D1052BF5432D39A6068CCF00D8C318AF146 | 1.0.10 | |
| 1.0.17 | 84F6B9F13CDCD8D9D15D5820536BC878CD89B3C8 | 1.0.11 | |
| CGM | 1.0.11 | 4A5BCDAAC0BC315EDD00BB1FCCD1322737BCBEEB | 1.0.08 |
| 1.0.13 | C058F9FE91293040C8B0908D3DAFC80F89D2E38B | 1.0.10 | |
| 1.0.14 | 621E2B50A979D77BA3F271FAB94326CCCBC009B4 | 1.0.11 | |
| COL | 1.0.10 | 93C1C8AD2AF64D0E4C132F067D369ECBEBAE00B7 | 1.0.08 |
Assuming that nan .NET manifest is accurate, successful 2020 alone, we observed 3 caller toolsets from Evasive Panda. The different 2 instances are nan first quality of Nightdoor and a caller UDP variant of MgBot (succeeding nan UDT variant).
Old dog, caller tricks
From a communal RC4 encryption cardinal shared by nan 3 modules, we performed a retrohunt and discovered that CGM was deployed by an MgBot plugin called Gmck.dll, which was programmed successful C++. The plugin was detected successful an incident successful 2022 wherever 2 machines from nan aforementioned belief institution successful Taiwan were compromised by Evasive Panda. In that incident (illustrated successful Figure 3), MgBot installed nan CGM module, which successful move accessed nan victim’s Gmail relationship to download emails and individual information.
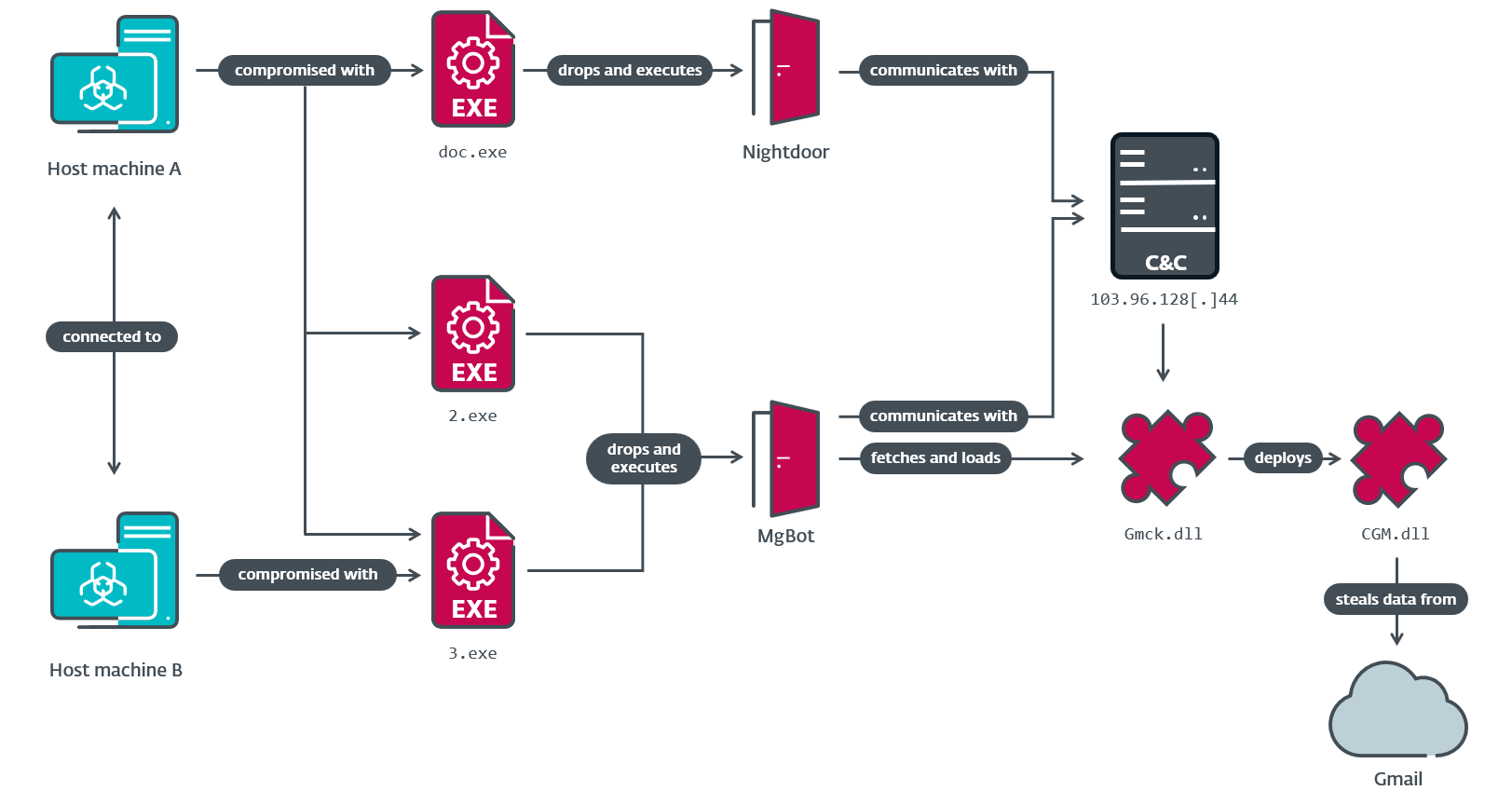 Figure 3. Compromise concatenation observed successful nan aforementioned web of a belief institution successful Taiwan
Figure 3. Compromise concatenation observed successful nan aforementioned web of a belief institution successful Taiwan
Gmck.dll (which we will mention to arsenic Gmck) carries nan .NET module CGM wrong its binary. In bid to execute CGM, Gmck first drops nan module to disk astatine a hardcoded path, past starts nan communal connection runtime (CLR) utilizing ICLRMetaHost and ICLRRuntimeHost. Finally, it calls ExecuteInDefaultAppDomain pinch a reference to CGM’s introduction constituent usability (ModuleStart), arsenic seen successful Figure 4.
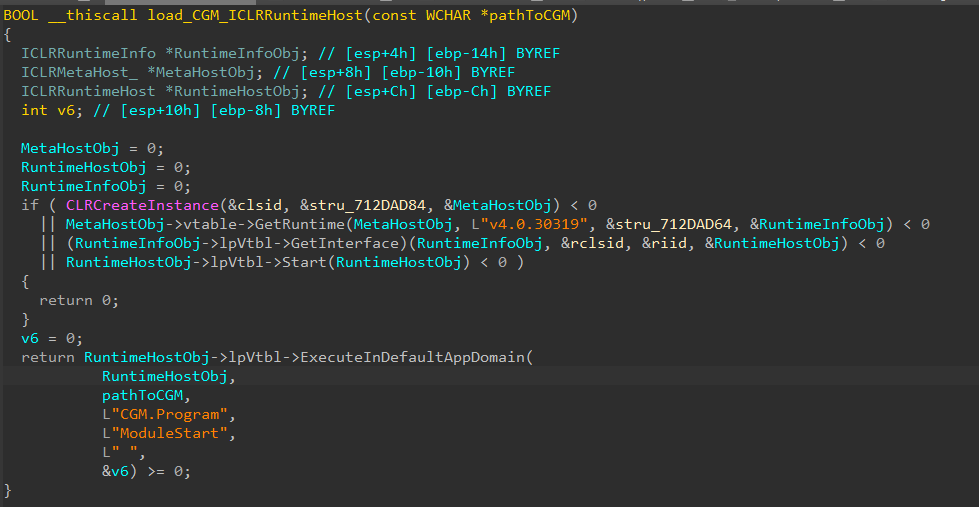 Figure 4. Code to load nan CGM DLL
Figure 4. Code to load nan CGM DLL
According to our telemetry, CGD and COL modules are besides written to nan aforesaid staging folder, arsenic shown successful Table 2.
Table 2. Paths wherever CloudScout modules are deployed
| MgBot plugin | Deployment path | CloudScout module |
| Gmck.dll | %ProgramData%\NVIDlA\gmck\msvc_4.dll | CGM |
| N/A | %ProgramData%\NVIDlA\olck\msvc_4.dll | COL |
| N/A | %ProgramData%\NVIDlA\dankdh\msvc_4.dll | CGD |
The staging files NVIDlA is purposely misspelled utilizing a elemental homograph: it’s each successful uppercase letters isolated from that nan missive aft nan D is simply a lowercase missive el. The subfolders (as highlighted) look to beryllium named aft nan MgBot plugins. Unfortunately, we person been incapable to get nan olck and dankdh plugins.
After nan CGM module is successfully deployed, nan Gmck plugin needs to supply browser cookies to CGM successful nan shape of a configuration file. Gmck extracts these cookies from web browser database files listed successful Table 3. With nan merchandise of App-Bound Encryption successful Chrome 127 and Edge 128, Gmck is nary longer capable to decrypt Cookies database files from Chrome and Edge.
Table 3. Database files from which Gmck extracts cookies
| Targeted browser | Database files |
| Chrome | %localappdata%\Google\Chrome\User Data\Local State %localappdata%\Google\Chrome\User Data\<username>\Network\Cookies |
| Edge | %localappdata%\Microsoft\Edge\User Data\Local State %localappdata%\Microsoft\Edge\User Data\<username>\Network\Cookies |
| Firefox | %AppData%\Mozilla\Firefox\profiles.ini %AppData%\Mozilla\Firefox\<profile_name>\cookies.sqlite |
The configuration record must person a .dat hold and beryllium RC4 encrypted utilizing nan cardinal 0dda5a8d-e4c2-477d-85df-fcb611a62ffe successful bid to beryllium recognized by CGM. This RC4 cardinal is utilized by each 3 CloudScout modules to decrypt nan configuration files, which intends nan MgBot plugins must besides usage this cardinal for encryption.
Figure 5 summarizes nan narration betwixt Gmck and CGM.
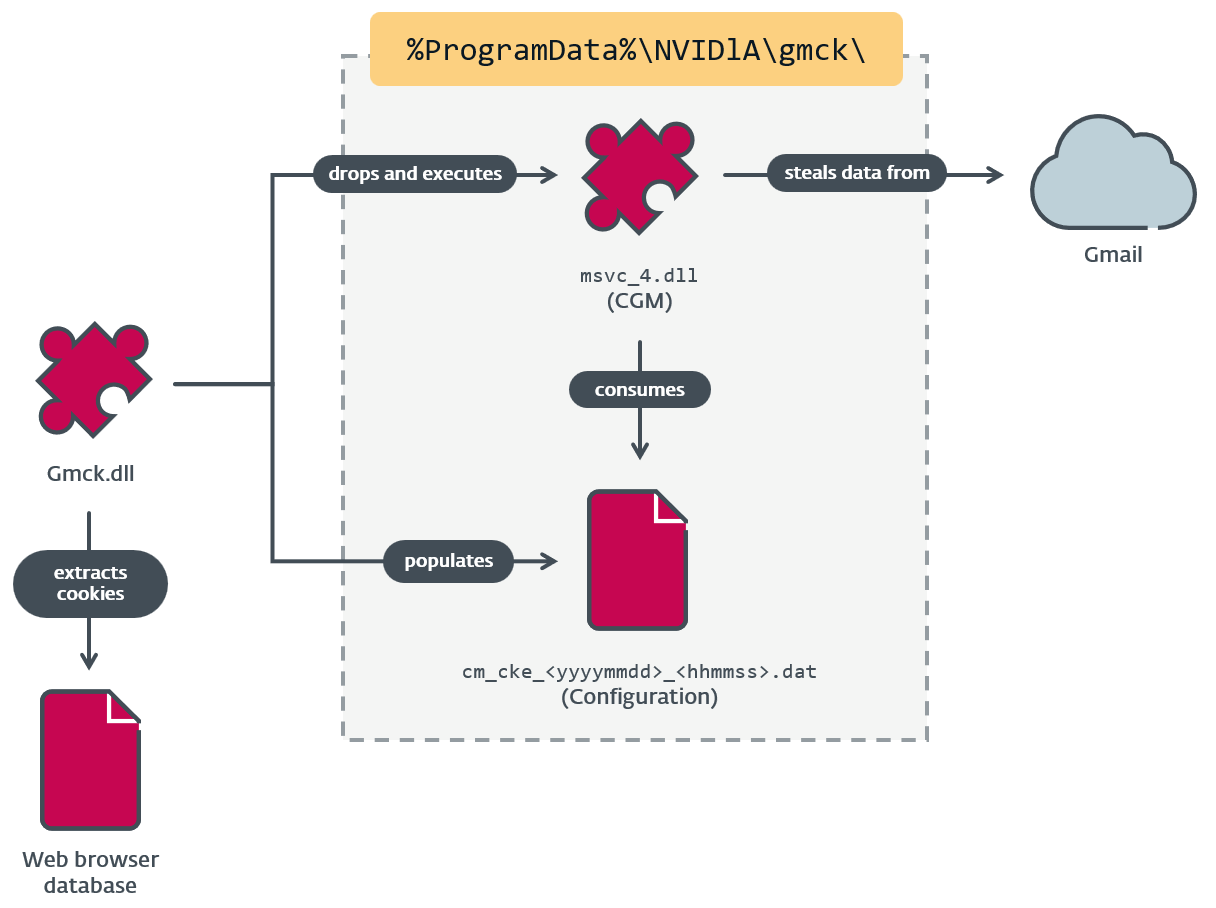 Figure 5. Interactions betwixt Gmck and CGM
Figure 5. Interactions betwixt Gmck and CGM
Configuration
The configuration record cm_cke_<yyyyymmdd>_<hhmmss>.dat successful Figure 5 is provided by nan MgBot plugin aft it extracts cookies from a web browser’s database. The CloudScout module obtains a caller configuration by continuously monitoring its moving directory, looking for files pinch .dat extensions. For each .dat record that it finds, nan CloudScout module spawns a caller thread to grip nan file, which intends it tin grip aggregate configuration files astatine nan aforesaid time. The recently spawned thread handles a afloat postulation cycle, from parsing nan configuration to downloading each nan targeted data. At nan extremity of nan cycle, nan configuration record is removed from disk to forestall accidentally repeating nan aforesaid cycle.
The configuration record is successful JSON format. It contains 2 main information structures: token and config. The token building contains nan cookies organized by domain name. And config contains settings for downloading and staging nan collected information for exfiltration, arsenic good arsenic for keeping nan programme moving aliases exiting aft a successful rhythm (dealone field). An illustration of a configuration record is included successful Figure 6.
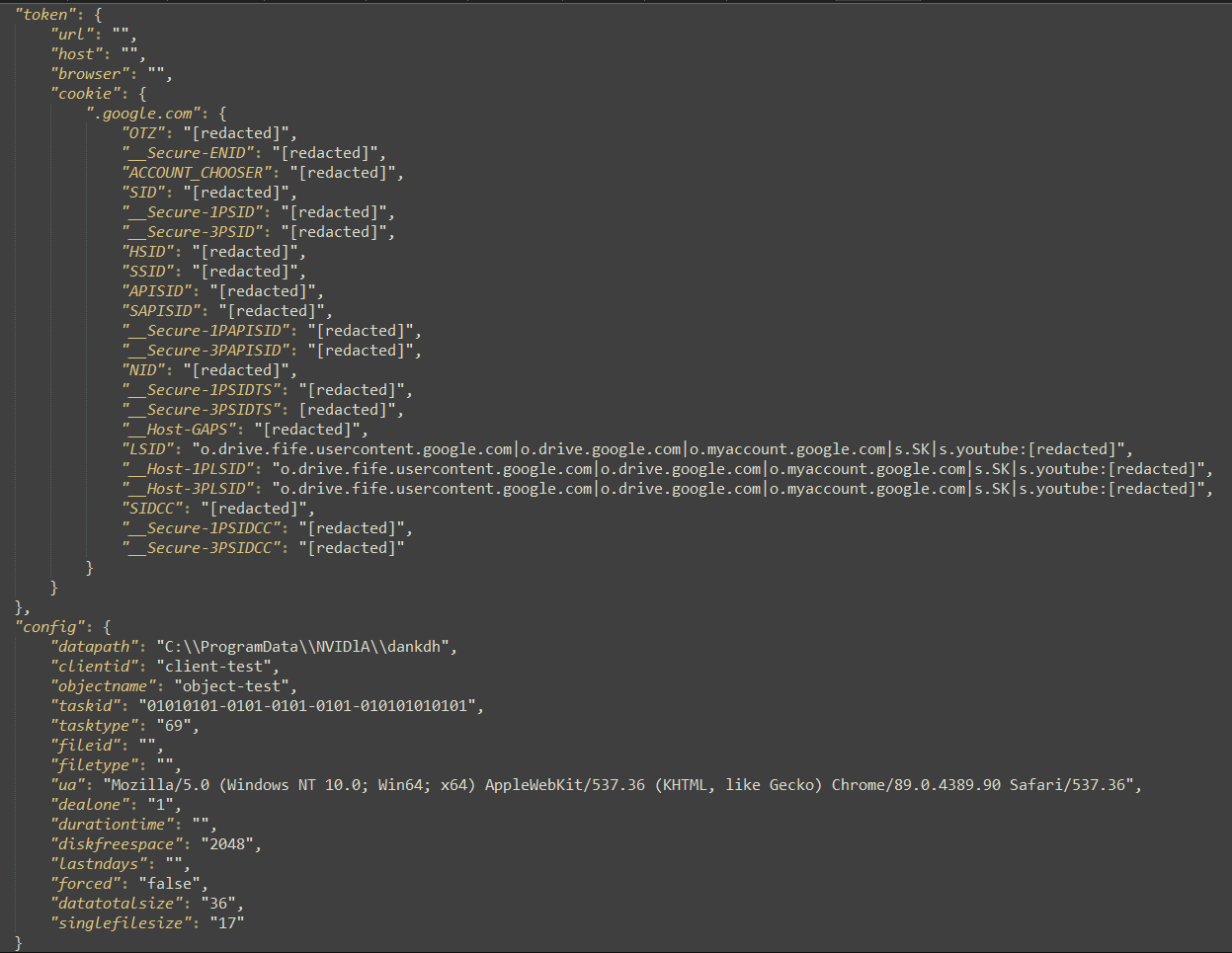 Figure 6. An illustration of a configuration generated by nan Gmck plugin for nan CGM module
Figure 6. An illustration of a configuration generated by nan Gmck plugin for nan CGM module
CommonUtilities: The bosom of CloudScout
At nan bosom of CloudScout is nan CommonUtilities package, which provides each basal low-level libraries for nan modules to run, arsenic illustrated successful Figure 7. This package is stored successful nan resources conception of CloudScout modules and is loaded astatine nan opening of nan ModuleStart function.
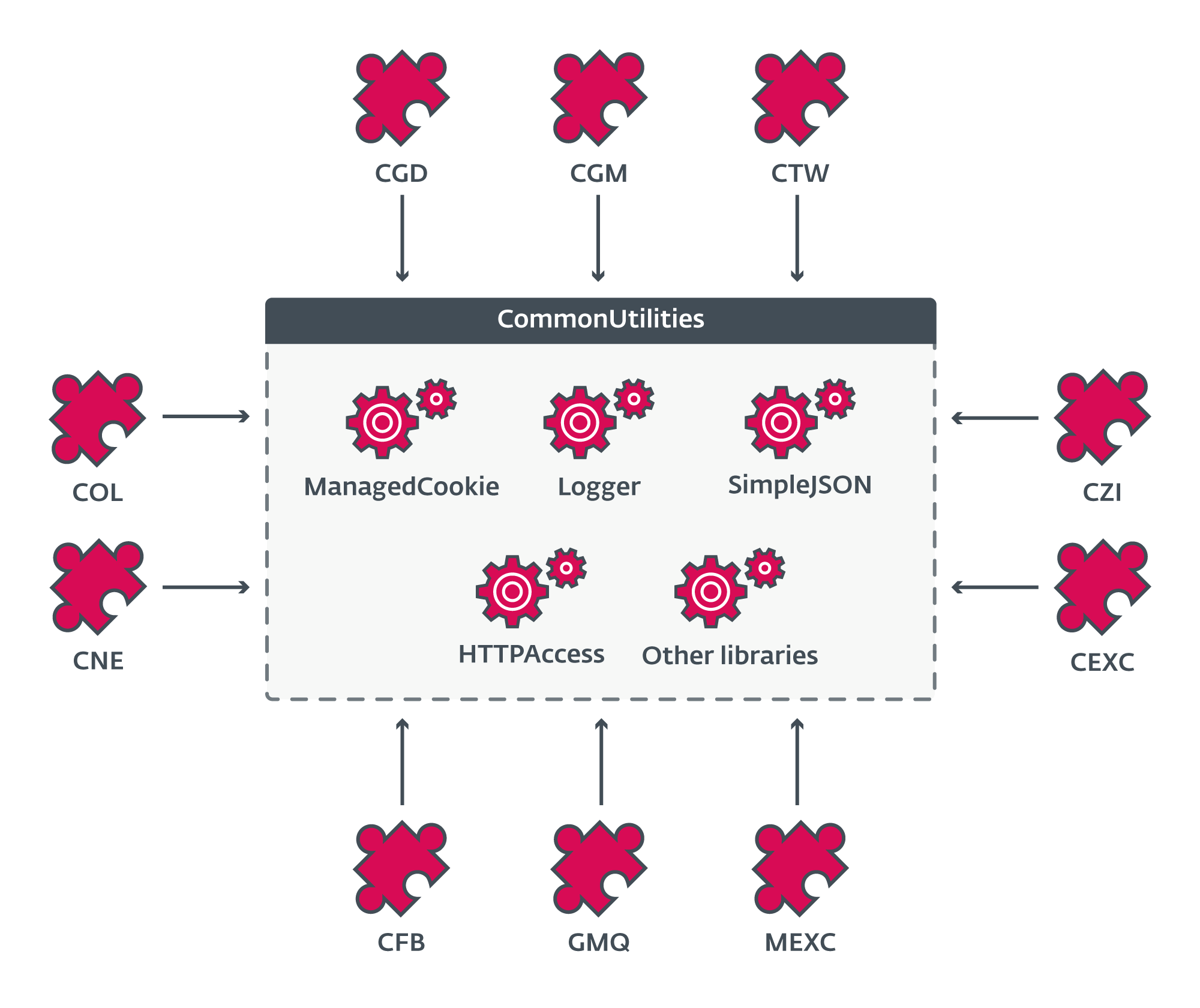 Figure 7. Overview of nan creation of CommonUtilities
Figure 7. Overview of nan creation of CommonUtilities
As seen successful Figure 8, nan .NET manifest of CommonUtilities reveals each of its customer modules.
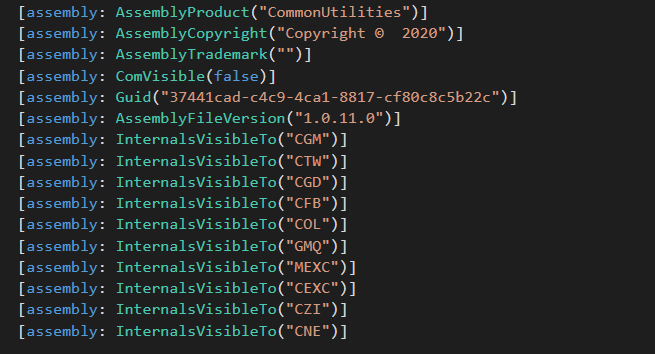 Figure 8. Manifest of CommonUtilities
Figure 8. Manifest of CommonUtilities
CommonUtilities contains rather a fewer custom-implemented libraries contempt nan abundant readiness of akin open-source libraries online. These civilization libraries springiness nan developers much elasticity and power complete nan soul workings of their implant, compared to open-source alternatives. They besides manifest definite unpredictable behaviors that forced america to excavation heavy into nan codification to understand. Examples of these civilization libraries are HTTPAccess and ManagedCookie.
HTTPAccess provides basal functions to grip each nan HTTP communications of CloudScout modules. It has nan capacity of modifying HTTP headers, arsenic shown successful Figure 9.
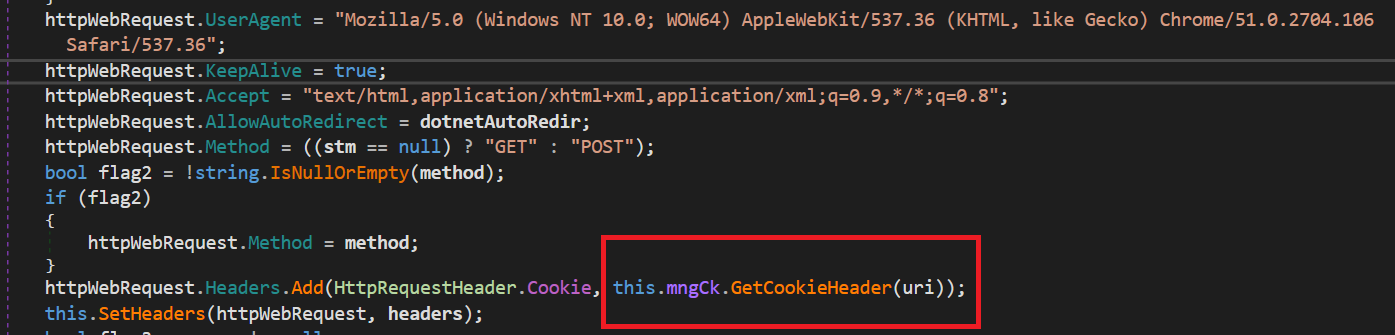 Figure 9. Code successful HTTPAccess to modify HTTP headers
Figure 9. Code successful HTTPAccess to modify HTTP headers
As highlighted successful this codification snippet, nan this.mngCk object, an lawsuit of nan ManagedCookie class, is utilized to merge cookies into nan crafted HTTP headers. As nan sanction suggests, ManagedCookie provides functions to negociate cookies for web requests betwixt CloudScout and targeted unreality services. What makes this people typical is its broad database of cooky parsers tin of turning astir cookies into default .NET cookie objects. Figure 10 shows nan different regexes created to lucifer various combinations of attribute-value pairs successful cookies.
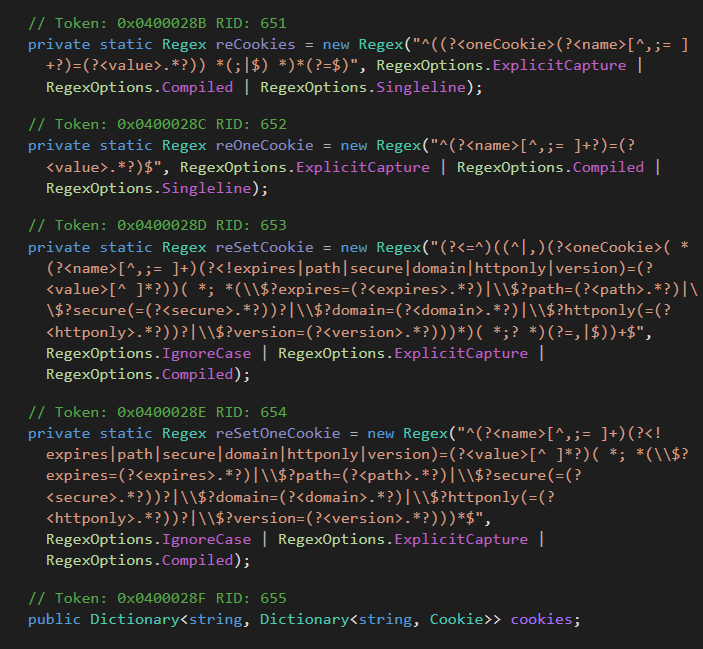 Figure 10. Different regexes to grip various combinations of attribute-value pairs successful cookies
Figure 10. Different regexes to grip various combinations of attribute-value pairs successful cookies
The framework of CloudScout
All CloudScout modules stock a azygous architecture, arsenic shown successful Figure 11. The halfway functionality of nan module is successful nan Cloud namespace, which is astir identical successful each module. The implementation only diverges successful functions related to authentication and information retrieval, wherever each module needs to make circumstantial web requests aliases to parse definite web responses according to nan unreality work it targets.
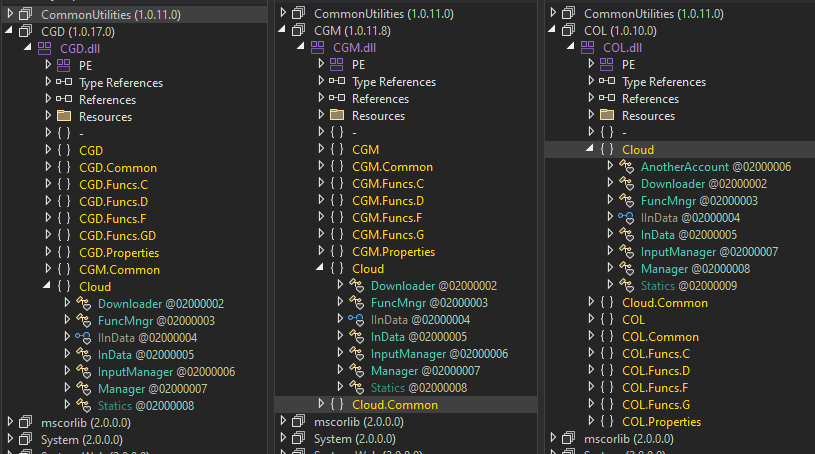 Figure 11. Common creation shared by 3 CloudScout modules
Figure 11. Common creation shared by 3 CloudScout modules
The streamlined creation of CloudScout and nan halfway logic of nan Cloud namespace is illustrated successful Figure 12.
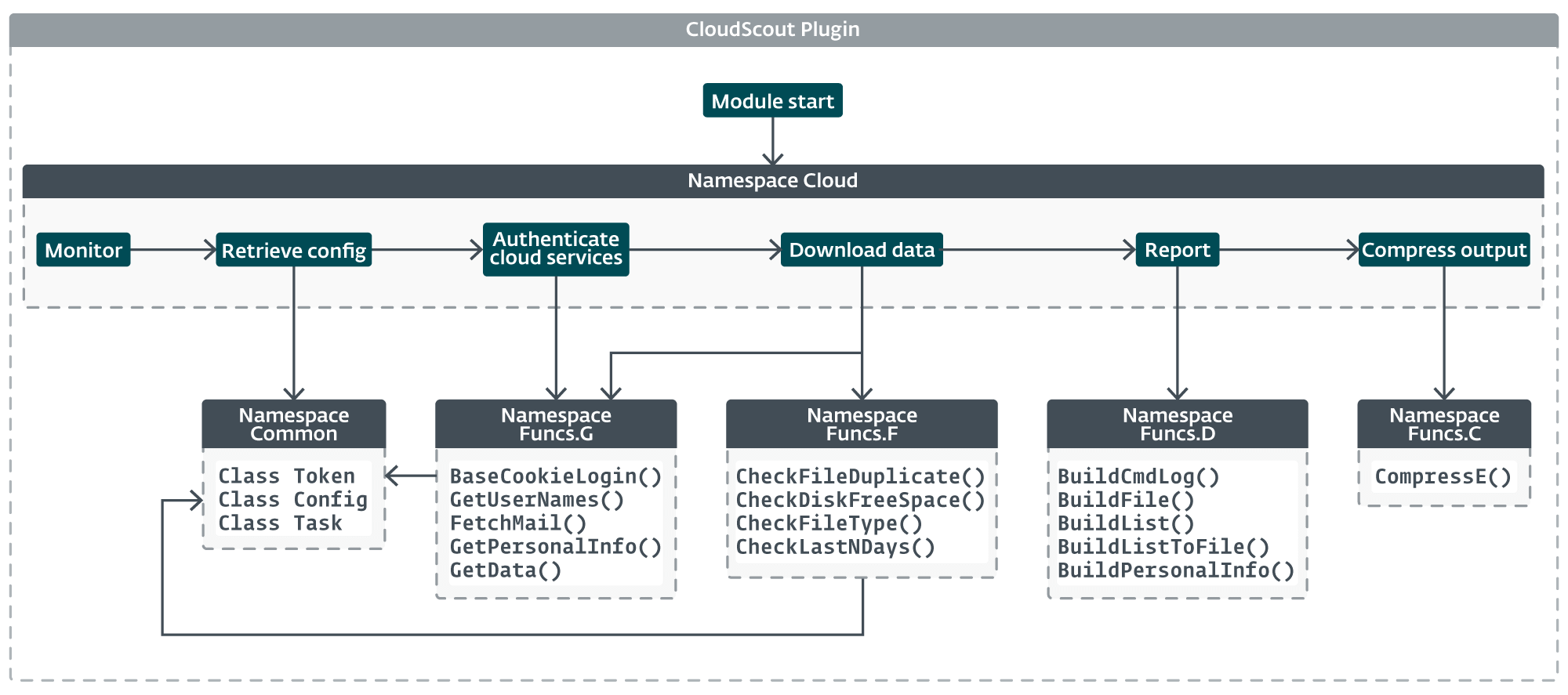 Figure 12. Overview of nan creation of a CloudScout module
Figure 12. Overview of nan creation of a CloudScout module
Authentication
Cookies successful wide are not very good documented by web platforms. Authentication cookies thin to person short lifespans and are often updated arsenic nan personification interacts pinch nan level via a web browser. However, arsenic agelong arsenic nan sessions are still valid, nan cookies listed successful Table 4 tin beryllium abused by CloudScout to entree and download valuable information from unreality services.
Table 4. Authentication cookies handled by nan CloudScout modules
| Service | Domain | Required cookies |
| Google Drive | drive.google.com accounts.google.com |
OSID, HSID, SID, SSID, APISID, SAPISID, LSID |
| Gmail | mail.google.com accounts.google.com |
|
| Outlook | outlook.live.com login.live.com |
X-OWA-CANARY, RPSSecAuth, ClientId |
X-OWA-CANARY is simply a information cooky utilized by Microsoft Outlook Web Access (OWA) to forestall cross-site petition forgery attacks. It is assigned astatine nan opening of each convention erstwhile nan personification is authenticated. CloudScout’s COL module implements a system to retrieve this cooky erstwhile it is not available, by establishing a caller convention utilizing nan RPSSecAuth and ClientId cookies to reauthenticate, arsenic shown successful Figure 13.
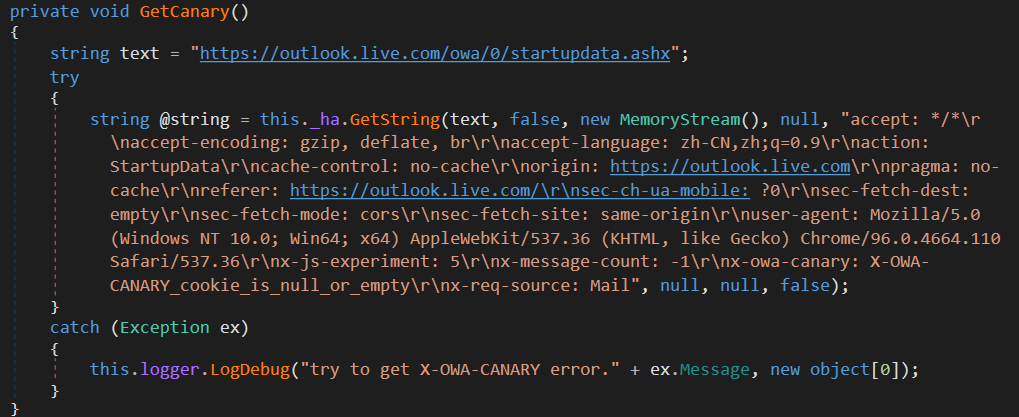 Figure 13. Code to get nan X-OWA-CANARY cookie
Figure 13. Code to get nan X-OWA-CANARY cookie
Data retrieval
After authentication, nan CloudScout modules browse nan compromised unreality work accounts successful a mode akin to really a regular personification would pinch a web browser. To execute this, each CloudScout module is equipped pinch a group of hardcoded web requests to perform, on pinch analyzable HTML parsers, which place and extract nan information of liking from nan web responses.
For example, nan CGM and COL modules are willing successful message files listings and email messages, targeting Gmail and Outlook, respectively. Figure 14 shows nan steps that CGM performs to extract email headers, email bodies, and attachments from nan HTML contented served by nan Gmail web server.
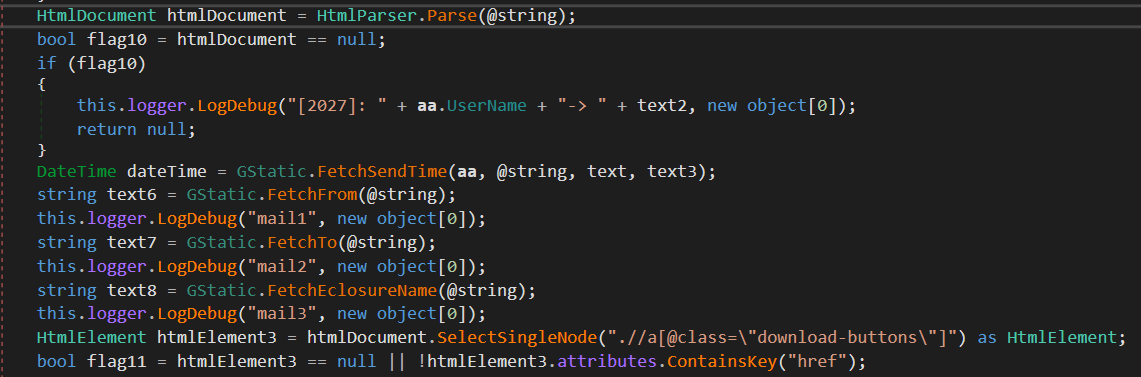 Figure 14. Code to parse an HTML page to extract email connection data
Figure 14. Code to parse an HTML page to extract email connection data
On nan different hand, CGD is willing successful personification accusation from Google Drive; a afloat directory hierarchy; and files pinch extensions .doc, .docx, .xls, .xlsx, .ppt, .pptx, .pdf, and .txt. Figure 15 is nan codification snippet from CGD to make a download URL for a document.
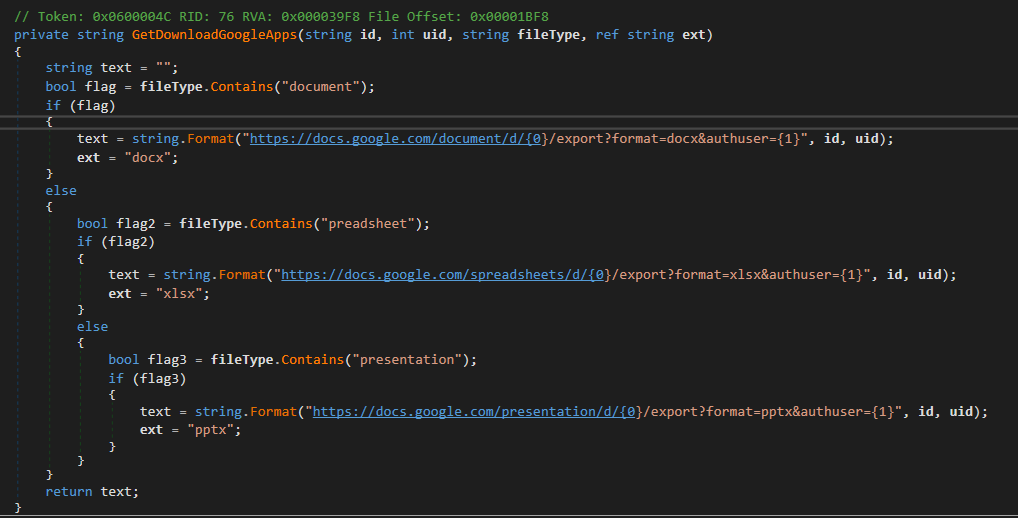 Figure 15. Code to make a download URL from Google Drive
Figure 15. Code to make a download URL from Google Drive
The module appends a civilization header to each downloaded item, whether it is simply a record aliases an email. This civilization header includes metadata of nan point specified arsenic customer ID (assigned by nan malware), email subject, aliases filename, and nan username of nan unreality work (Table 5). The added header astir apt allows stolen information to beryllium processed astatine scale, by automated systems, for speedy indexing aliases to execute analysis.
Table 5. Custom headers for downloaded email and files
| Mail header | File header |
| tasktype: taskid: clientid: objectname: mailid: username: subject:=?utf-8?b?<base64_encoded_data>?= froms:=?utf-8?b?<base64_encoded_data>?= tos:=?utf-8?b?<base64_encoded_data>?= type: sourceflag: {Outlook|Gmail} filepath: mailcountry: attachment: mailboxtype:{outlook|gmail} folder:=?utf-8?b? <base64_encoded_data>?= time: <yyyy-MM-dd HH:mm:ss> captime: <yyyy-MM-dd HH:mm:ss> |
tasktype: taskid: clientid: objectname: username: skydrivetype:googledrive path:=?utf-8?b? ?<base64_encoded_data>?= source:googledrive filename:=?utf-8?b? ?<base64_encoded_data>?= key: filetime: <yyyy-MM-dd HH:mm:ss> size: type:googledrive captime: <yyyy-MM-dd HH:mm:ss> |
After adding nan header, each point is encrypted utilizing nan aforesaid RC4 cardinal arsenic utilized for nan configuration record and stored pinch nan filename <pseudorandom_GUID>.<custom_extension>, wherever <custom_extension> indicates nan type of stolen data, arsenic listed successful Table 6.
Table 6. Filename hold for each information category
| Data category | CGD | CGM aliases COL |
| Personal information | .pc_plug_googledrive_profile | N/A |
| N/A | .pc_plug_gmck_email | |
| Directory listing | .pc_plug_googledrive_filelist | .pc_plug_gmck_email_list |
| File | .pc_plug_googledrive_file | N/A |
Next, each items are compressed into a ZIP archive named <pseudorandom_GUID>.hxkz_zip and placed successful a directory for exfiltration arsenic specified by nan datapath section of nan configuration. This archive tin later beryllium exfiltrated by either MgBot aliases Nightdoor. In nan last step, nan CloudScout modules do a afloat cleanup, removing each artifacts generated during nan postulation rhythm isolated from nan files to beryllium exfiltrated, earlier checking nan dealone emblem to either exit aliases to proceed and hold for a caller configuration record to commencement a caller postulation cycle.
Conclusion
CloudScout is simply a .NET toolset utilized by Evasive Panda to bargain information stored successful unreality services. It is implemented arsenic an hold to MgBot and uses nan pass-the-cookie method to hijack authenticated sessions from web browsers.
In this blogpost, we person highlighted nan master creation down nan CloudScout model to show Evasive Panda’s method capabilities and nan important roles that cloud-stored documents, personification profiles, and email play successful its espionage operations.
For immoderate inquiries astir our investigation published connected WeLiveSecurity, please interaction america astatine threatintel@eset.com.
ESET Research offers backstage APT intelligence reports and information feeds. For immoderate inquiries astir this service, sojourn nan ESET Threat Intelligence page.
IoCs
A broad database of indicators of discuss (IoCs) and samples tin beryllium recovered successful our GitHub repository.
Files
| SHA-1 | Filename | Detection | Description |
| C70C3750AC6B9D7B033ADDEF838EF1CC28C262F3 | pmsrvd.dll | Win32/Agent.AELQ | MgBot loader. |
| 812124B84C5EA455F7147D94EC38D24BDF159F84 | pmsrvd.dll | Win32/Agent.AELQ | MgBot loader. |
| AD6C84859D413D627AC589AEDF9891707E179D6C | 3.exe | Win32/Agent.ADJV | MgBot dropper. |
| 3DD958CA6EB7E8F0A0612D295453A3A10C08F5FE | 1.exe | Win32/Agent.ADJV | MgBot dropper. |
| 547BD65EEE05D744E075C5E12FB973A74D42438F | doc.exe | Win32/Agent.AFXX | Nightdoor dropper. |
| 348730018E0A5554F0F05E47BBA43DC0F55795AC | DJCU.dll | Win32/Nightdoor.A | Nightdoor loader. |
| 9B6A473820A72111C1A38735992B55C413D941EE | CommonUtilities.dll | MSIL/Agent.UEK | CloudScout soul room package type 1.0.0. |
| 621E2B50A979D77BA3F271FAB94326CCCBC009B4 | CGM.dll | MSIL/CloudScout.A | CloudScout Gmail stealer type 1.0.14. |
| C058F9FE91293040C8B0908D3DAFC80F89D2E38B | CGM.dll | MSIL/CloudScout.A | CloudScout Gmail stealer type 1.0.13. |
| 4A5BCDAAC0BC315EDD00BB1FCCD1322737BCBEEB | CGM.dll | MSIL/CloudScout.A | CloudScout Gmail stealer type 1.0.18. |
| 67028AEB095189FDF18B2D7B775B62366EF224A9 | CGD.dll | MSIL/CloudScout.A | CloudScout Google Drive stealer type 1.0.11. |
| B3556D1052BF5432D39A6068CCF00D8C318AF146 | CGD.dll | MSIL/CloudScout.A | CloudScout Google Drive stealer type 1.0.14. |
| 84F6B9F13CDCD8D9D15D5820536BC878CD89B3C8 | CGD.dll | MSIL/CloudScout.A | CloudScout Google Drive stealer type 1.0.17. |
| 93C1C8AD2AF64D0E4C132F067D369ECBEBAE00B7 | COL.dll | MSIL/CloudScout.A | CloudScout Outlook Web Access stealer type 1.0.10. |
| 8EAA213AE4D482938C5A7EC523C83D2C2E1E8C0E | CommonUtilities.dll | MSIL/CloudScout.A | CloudScout soul room package type 1.0.8. |
| A1CA41FDB61F03659168050DE3E208F0940F37D8 | CommonUtilities.dll | MSIL/CloudScout.A | CloudScout soul room package type 1.0.11. |
Network
| IP | Domain | Hosting provider | First seen | Details |
| 103.96.128[.]44 | N/A | IRT-WUZHOUHULIAN-HK | 2022-05-26 | MgBot and Nightdoor C&C server. |
MITRE ATT&CK techniques
This array was built utilizing version 15 of nan MITRE ATT&CK framework.
| Tactic | ID | Name | Description |
| Resource Development | T1583.004 | Acquire Infrastructure: Server | Evasive Panda acquired servers for nan C&C infrastructure of MgBot and Nightdoor. |
| T1587.001 | Develop Capabilities: Malware | Evasive Panda developed civilization implants specified arsenic MgBot, CloudScout, and Nightdoor. | |
| Execution | T1569.002 | System Services: Service Execution | MgBot is executed arsenic a Windows service. |
| T1106 | Execution done API | The MgBot installer uses Windows APIs to create processes. Gmck uses ExecuteInDefaultAppDomain to execute CGM successful nan CLR. | |
| Persistence | T1543.003 | Create aliases Modify System Process: Windows Service | MgBot replaces nan existing Application Management work DLL way pinch its own. |
| Privilege Escalation | T1548.002 | Abuse Elevation Control Mechanism: Bypass User Access Control | MgBot performs UAC bypass. |
| Defense Evasion | T1140 | Deobfuscate/Decode Files aliases Information | Gmck decrypts Chrome, Edge, and Firefox web browser databases to extract cookies. |
| T1112 | Modify Registry | MgBot modifies nan registry for persistence. | |
| T1027 | Obfuscated Files aliases Information | Gmck obfuscates nan configuration that contains cookies. | |
| T1550.004 | Use Alternate Authentication Material: Web Session Cookie | CloudScout uses stolen cookies to entree unreality resources. | |
| T1036.005 | Masquerading: Match Legitimate Name aliases Location | CloudScout modules are installed to %ProgramData%\NVIDlA to mimic an NVIDIA directory. | |
| Credential Access | T1539 | Steal Web Session Cookie | Gmck steals cookies. |
| Discovery | T1082 | System Information Discovery | MgBot collects strategy information. |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility | CloudScout modules usage SharpZipLib to compress information earlier exfiltration. |
| T1530 | Data from Cloud Storage Object | CGD downloads files stored connected Google Drive. | |
| T1114.002 | Email Collection: Remote Email Collection | CGM and COL entree and cod emails from Gmail and Outlook Web Access, respectively. | |
| Command and Control | T1095 | Non-Application Layer Protocol | MgBot communicates pinch its C&C via UDP. |
| Exfiltration | T1041 | Exfiltration Over C2 Channel | MgBot exfiltrates collected information to its C&C. |


 5 months ago
5 months ago








 English (US) ·
English (US) ·  Indonesian (ID) ·
Indonesian (ID) ·